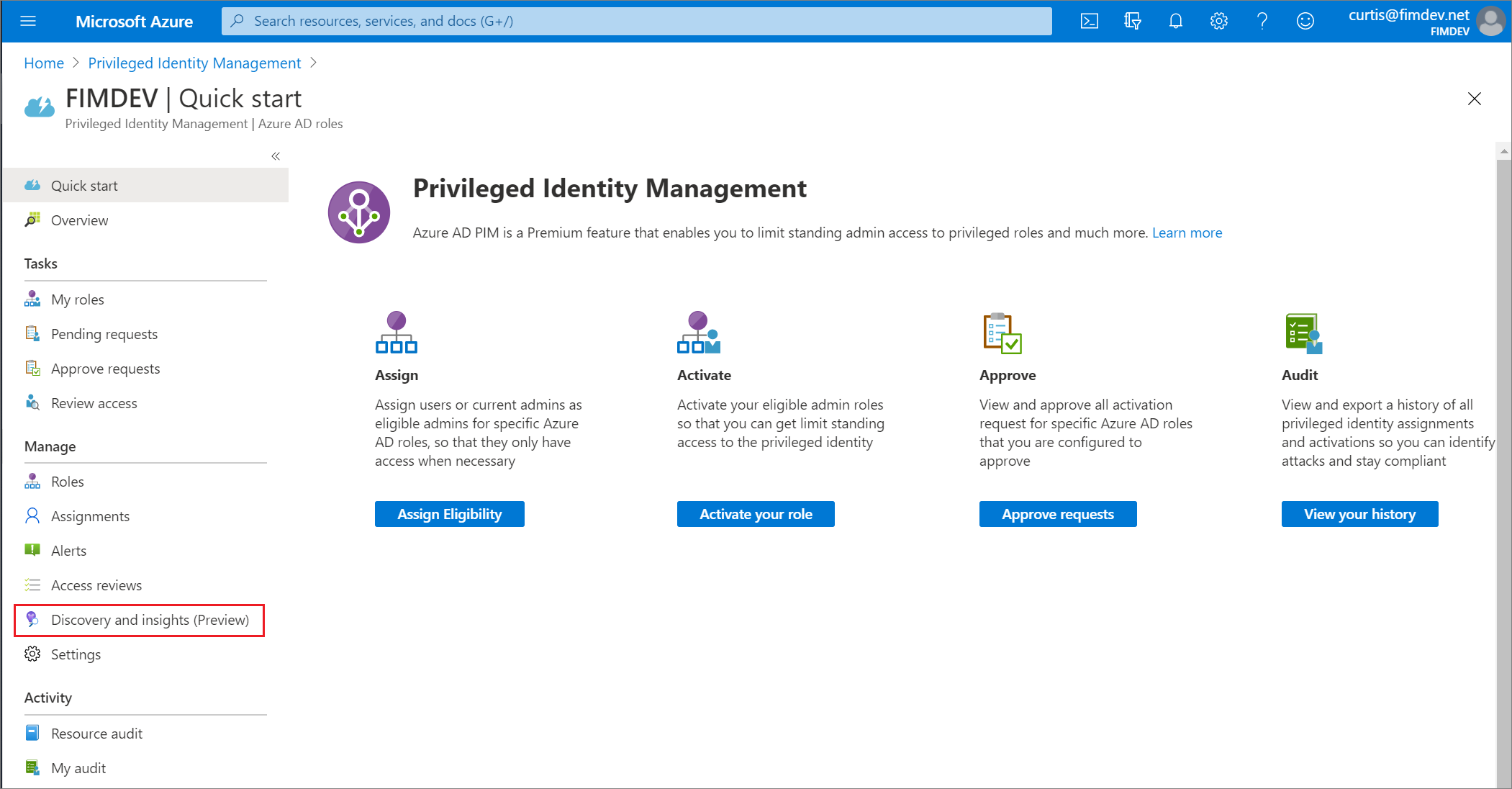
Azure AD roles Discovery and insights (preview) in Privileged Identity Management former Security Wizard - Microsoft Entra | Microsoft Learn

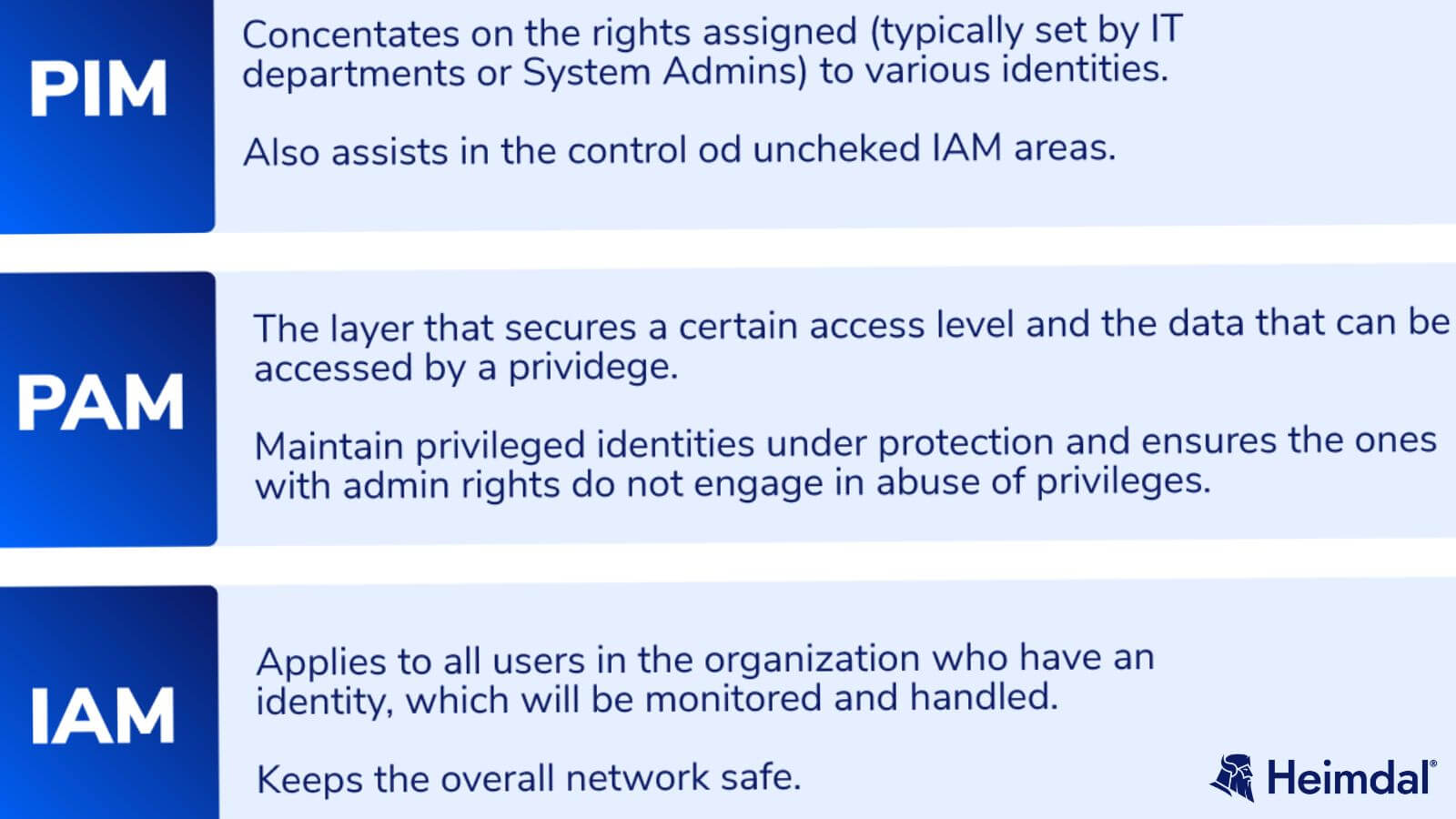
Privileged identity management software solutions for enterprise|PIM suite - ManageEngine Password Manager Pro

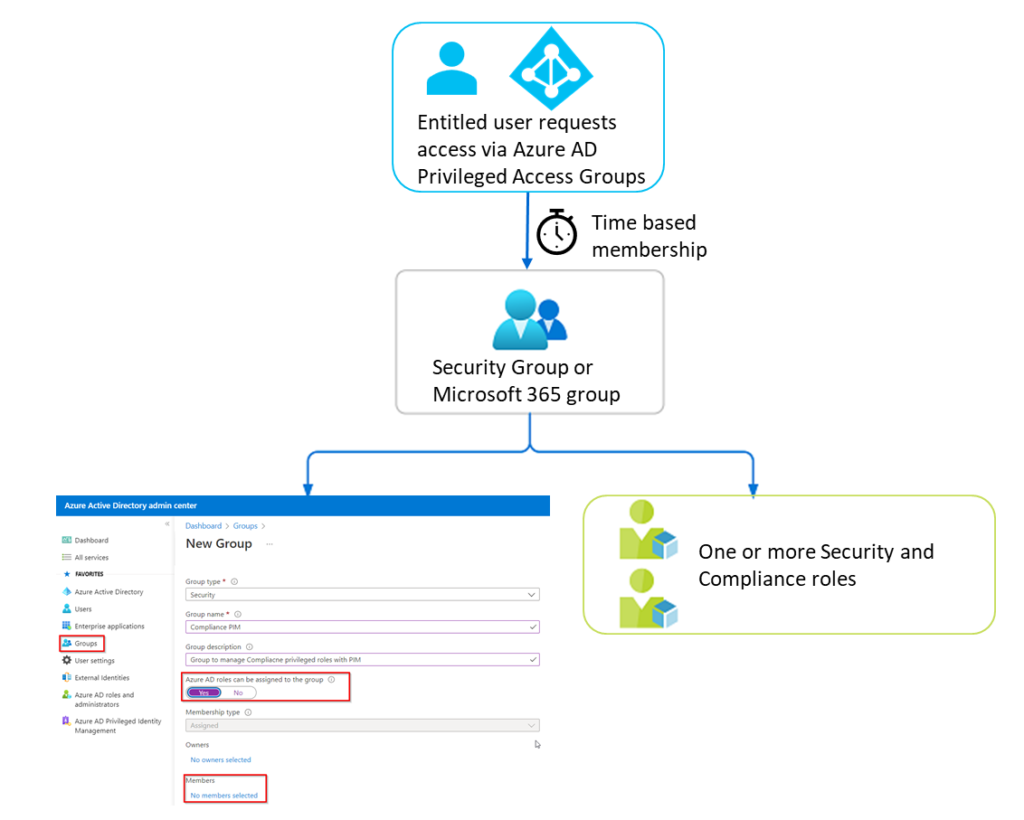
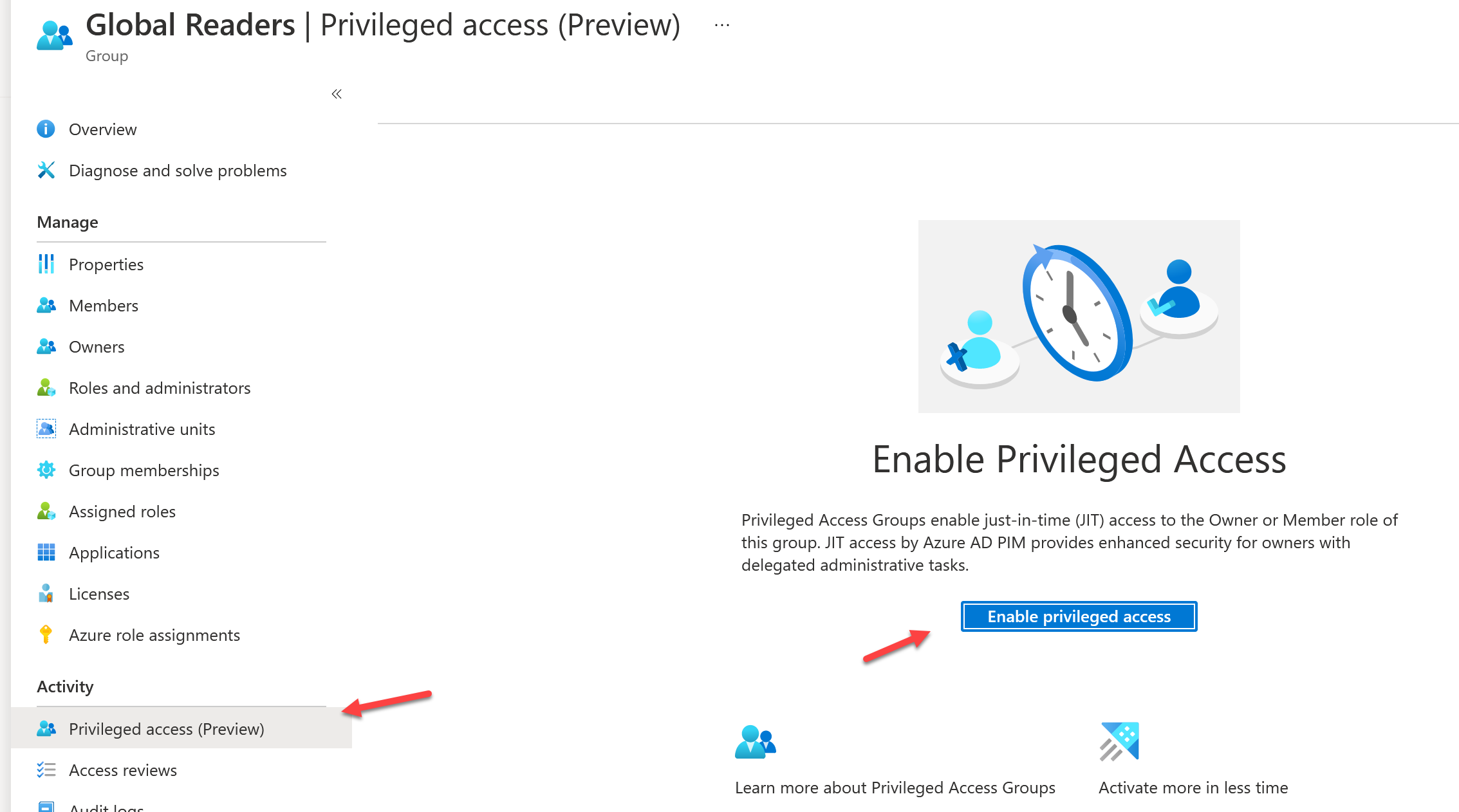
Using PIM Groups and Azure Key Vault as a Secure, Just in Time, Password Management Solution – Sean McAvinue














.png)